Microsoft's AI-powered Windows Recall feature, designed to capture and index user activity for an interactive timeline, is once again under intense scrutiny from cybersecurity experts. Originally slated for release on Copilot+ AI PCs in June 2024, the feature encountered several delays due to privacy concerns. While Microsoft has since revamped its design, security researchers are re-issuing warnings, indicating that the alleged vulnerabilities persist.
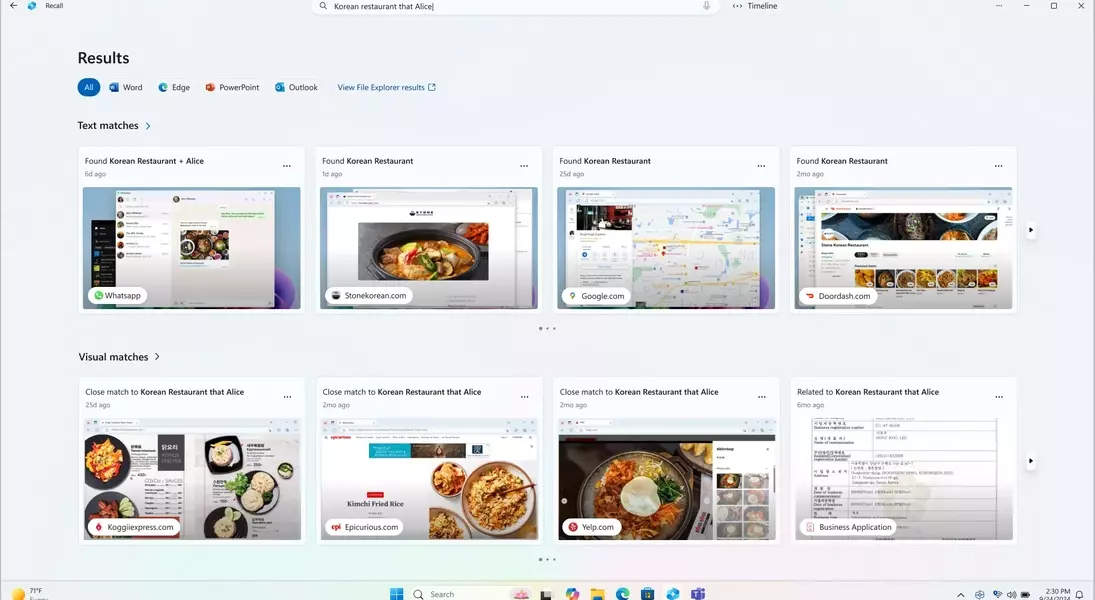
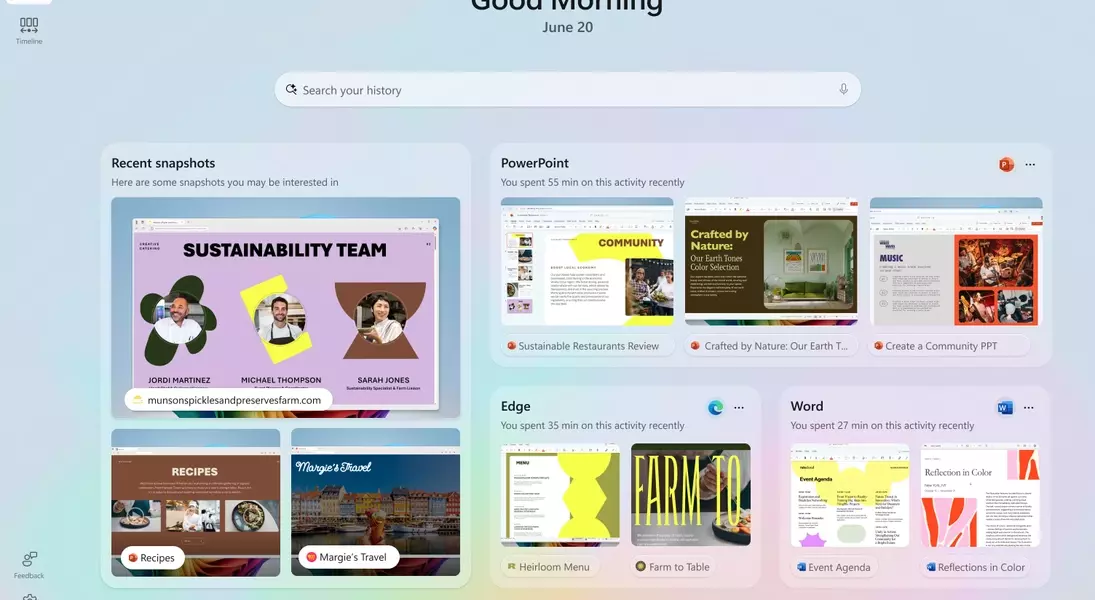
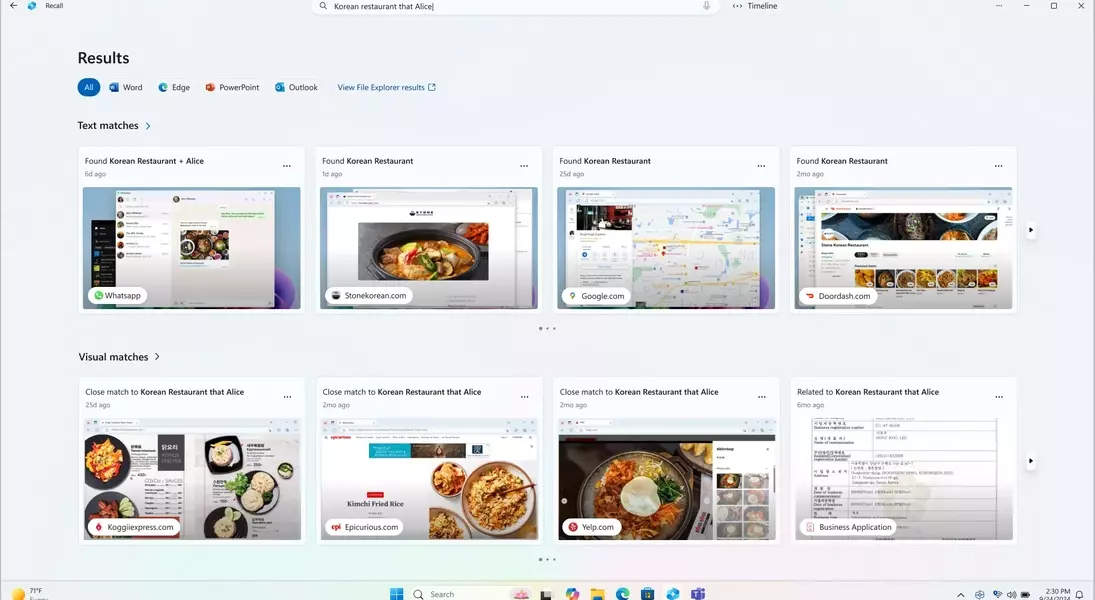
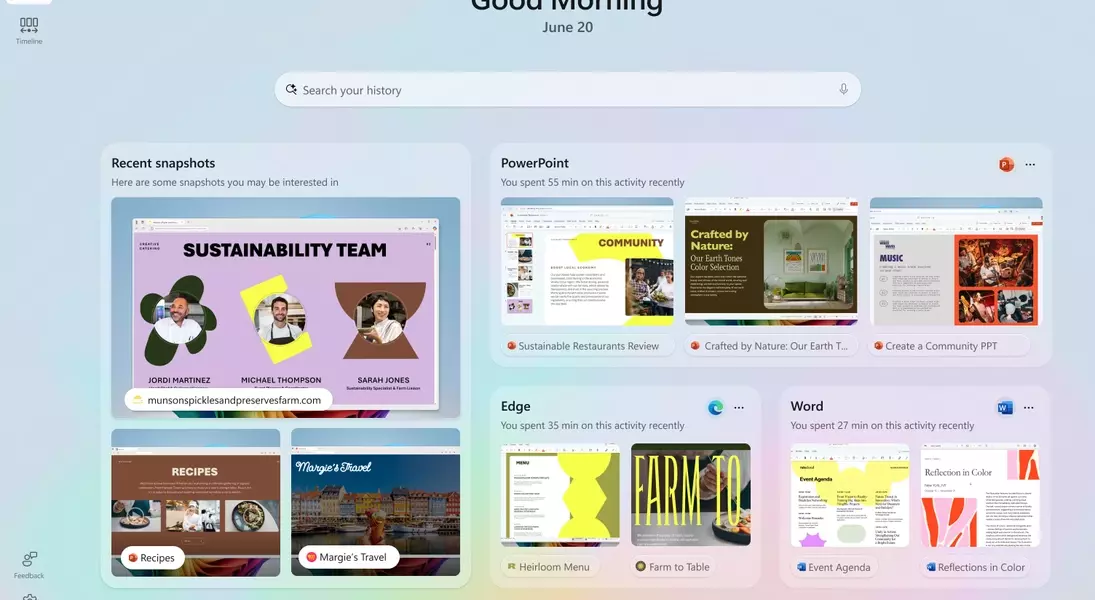
The core of Windows Recall involves continuously taking screenshots of a user's desktop, enabling them to navigate back through their past activities. Microsoft previously stated that these snapshots and related data would be safeguarded within a 'secure VBS Enclave'—a protected environment accessible only after user authentication via Windows Hello. This architecture was intended to prevent unauthorized access, even from malicious software. However, security researcher Alexander Hagenah has developed a tool, 'TotalRecall Reloaded,' that reportedly bypasses these protections, raising serious questions about the feature's real-world security.
Hagenah's tool operates by leveraging a user's legitimate access to the Recall timeline. When a user authenticates with Windows Hello to view their activity, TotalRecall Reloaded can reportedly intercept and extract the entire contents of the 'secured' vault. This directly contradicts Microsoft's claim that its security model would restrict such actions, particularly those by 'latent malware trying to ‘ride along’ with a user authentication to steal data.'
The researcher disclosed his findings to Microsoft last month, but, surprisingly, the company deemed his discovery 'not a vulnerability.' David Weston, Corporate Vice President of Microsoft Security, explained that the access patterns demonstrated align with 'intended protections and existing controls' and do not constitute a bypass of a security boundary or unauthorized data access. He also pointed to time-outs and anti-hammering protections as safeguards against malicious queries.
This stance from Microsoft is particularly perplexing given the breadth of data Recall collects, which can include browsing histories, emails, private messages, and other sensitive information displayed on the screen. Hagenah contends that the issue isn't with the cryptographic security of the 'vault' itself, but rather with the process of decrypting and rendering this content in an unprotected environment. He aptly summarized the situation, stating, 'The vault door is titanium. The wall next to it is drywall.'
Essentially, while the storage mechanism might be robust, the vulnerability arises when the data is brought out of the secure enclave for user interaction. Microsoft's reliance on biometric prompts for access might deter some attacks, but it doesn't address the fundamental flaw in how the data is handled once authenticated. A truly comprehensive solution would likely necessitate a significant re-architecture of the operating system's underlying processes to ensure that decrypted content remains protected throughout its lifecycle.
